Site Content
Digis Voice Entry System
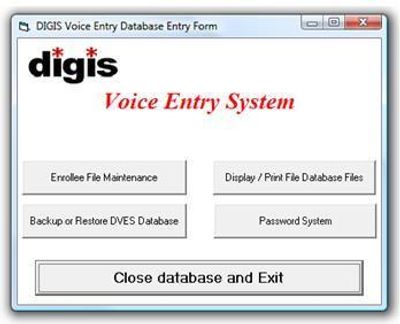
DVES is a computer aided voice biometric verification system consisting of various hardware, software, and licenced biometric components.
The components include:
A PC containing a "PCI" telephony card, The analog phone lines that connect to the ports of the card. A voice biometric software component that requires a licence. An application that is initiated by a phone call into the system. An application that creates, edits, and maintains the database information and voice print.
Upon configuration and execution of The "DVES" system, it will wait for a call. Caller information should have been previously enrolled (entered into the database of users). If the database does not contain any user records, the system will simply terminate the call. Enter one or more users (callers) into the database using the “DVES database” application ‘DVESDB’. This application requires several pieces of information to be input into the database. This includes badge number, PIN, Name etc .... and a request for a voice print. Once a user has been enrolled in the database, that user may call the computer. The computer requests a badge number along with a PIN that is to be entered using the telephone keypad. The information will be looked up in the database and if it exists, a request for a phrase from the caller will be asked for. The phrase should contain a few words that will be requested on all subsequent calls from this caller. Use at least 4 or 5 words in the phrase. The system will listen for 2 seconds. The phrase will be requested several times while the computer calculates a voice biometric. The voice biometric will be used for future verification and identification of this caller. The voice print is established and will be maintained in the database along with the other information for the caller. The next time the user calls the computer, a badge number is requested and looked up in the database. Since the voice print is now on file, it can be compared with the requested phrase that the computer will ask for. The phrase may be asked for again if the computer needs to recheck the phrase. Once the caller has been identified and verified as a legitimate entrant, one of two possibilities will occur. If the one man entry has been configured, the call will be transferred to an operator. If a two man entry is configured, the computer will say “Pass the phone to the second person”. The voive biometric for the second person will be verified (or rejected). Upon successful verification, the call will be transferred and entry will be permitted.
Copyright © 2020 DIGIS.COM - All Rights Reserved.
Powered by GoDaddy